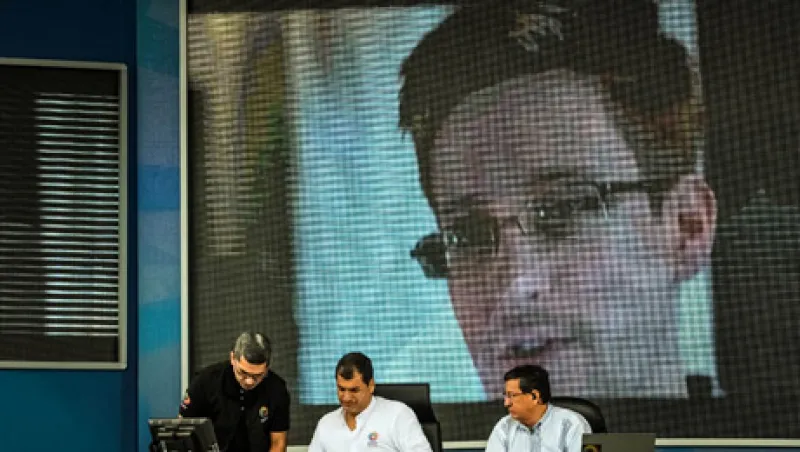
Information leakage — the loss of sensitive data — is a top concern of computer security experts. One such specialist, Edward Snowden, was obviously not in prevention mode last spring when he released classified National Security Agency documents through the news media. Amid the ensuing controversy over government surveillance, some collateral damage befell Snowden’s most recent employer, Booz Allen Hamilton.
The McLean, Virginia–based consulting company may have allayed serious reputational embarrassment by disclosing that it had employed the fugitive systems analyst for less than three months and terminated him on June 10 after the alleged misdeeds came to light.
Before Snowden went rogue — and easily overlooked as the scandal unfolded — was a promising new approach to cybersecurity championed by, among others, Booz Allen. The emphasis is on predictive intelligence in anticipation of threats, rather than the Whac-A-Mole approach of reacting to those that surface. Instead of constantly “defending the castle wall,” organizations focus on understanding attackers and their motivations and obtaining insight on when, where and how they will strike, explains Randy Hayes, head of Booz Allen’s predictive intelligence business.
This is a far cry from information security’s legacy of “playing catch-up,” notes Charles Iheagwara, director of the cybersecurity practice at Bethesda, Maryland–based consulting firm Unatek. He advocates “holistic system thinking” that results in an “adaptive security posture” to “stay ahead of the threat vectors” — all of which aligns with predictive intelligence principles, he said in a recent Massachusetts Institute of Technology webinar.
Although Booz Allen was not alone in seeking to define a new paradigm, it positioned itself in the vanguard in February with the launch of Cyber4Sight Threat Intelligence Services. The company invested $50 million over several years in a system of human and automated analytics that “ensures an organization stays one step ahead of its attackers,” according to Booz Allen vice chairman and former U.S. director of national intelligence John (Mike) McConnell.
Predictive intelligence is generating uncharacteristic optimism in an industry that was seemingly resigned to fighting a Hundred Years’ War against forces that never fail to find new weaknesses to exploit.
“We see more understanding of threat actors and their motivations, the techniques they use, and we have a better ability to customize controls for those techniques,” observes Joseph Nocera, leader of PricewaterhouseCoopers’ financial services information technology security and risk practice.
Predictive intelligence providers — a growing list that includes Booz Allen, CrowdStrike, Cyveillance, General Dynamics Fidelis Cybersecurity Solutions, GuruCul and Science Applications International Corp. — promise near-real-time analyses and advance warnings on a 24-7 basis. “It is not hard to find intelligence at a reasonable cost,” says Nocera. He is more concerned about companies’ ability to digest data and prioritize responses.
“Security really is a big-data problem,” adds the PwC consultant, referring to another contemporary challenge that technologists and corporations are gradually getting their arms around. Booz Allen says it sweeps and filters data from 55,000 global news sources, 16 social media feeds, 30 million blogs and microblogs and 500,000 message boards in 65 languages, while monitoring in real time 90,000 threats in a continuously updated malicious-code database.
“Big-data tools are helping to provide a richer picture of the threat matrix,” says Ernst & Young information security adviser George (Chip) Tsantes. “These are early days, but a number of vendors are enhancing these tools, and most of my bigger clients are at least working on pilots to coordinate these programs.”
Prolexic Technologies, a Hollywood, Florida, company focused specifically on the cyberattack known as distributed denial of service, says big-data streams must be distilled into real-time analytics for fast and effective threat identification and mitigation. Still, the process also requires experienced engineers to draw meaningful conclusions, says a recent Prolexic white paper.
“The fact is, leaders in the banking, health care and defense sectors are already embracing the newer breed of data protection services,” says Mark Bower, who oversees product management and solutions architecture for data encryption company Voltage Security, in Cupertino, California. “With the new, data-centric security approach, the table is turned” on the attackers.
There will be no end to the threats of malware and hacking, state-sponsored attacks and cyberterrorism. But the data indicates that some battles are winnable. • •
Jeffrey Kutler is editor-in-chief of Risk Professional magazine, published by the Global Association of Risk Professionals.