If there is one certainty when it comes to cybersecurity, it’s that things will get worse before they get better. So it is unsettling that September’s data breaches look like a nadir.
Within two weeks that month, Equifax said a massive hack exposed the personal information of 143 million Americans and the Securities and Exchange Commission disclosed that nonpublic corporate data in its Electronic Data Gathering, Analysis and Retrieval system, known as EDGAR, had been compromised. It’s hard to say which was worse.
While Equifax sent consumers into a tizzy, the credit-reporting company’s customers have other places to turn. The SEC, by contrast, is a federal regulator tasked with overseeing markets and protecting investors. Its role is critical to capital formation and wealth creation in the U.S. economy.
That’s why it was so disconcerting when the SEC revealed September 20 “that an incident previously detected in 2016 may have provided the basis for illicit gain through trading.” The breach made plausible long-held fears that U.S. markets and national security are vulnerable to codebreakers who may be enemies of the state.
“Cyber criminals could have manipulated the entire stock market and made billions of illicit profit,” says Ilia Kolochenko, chief executive officer of web security company High-Tech Bridge. “Ethical investors, including pension and sovereign funds, without the insider information could have lost fortunes as a result.”
Kolochenko says he worries that law enforcement is “catastrophically underfinanced” in the face of increasingly dire and sophisticated threats. Aware of the peril, officials have repeatedly called for the government and private sector to work together to increase cybersecurity.
“Cyber is the sole arena where private companies are the front line of defense in a nation-state attack on U.S. infrastructure,” the National Infrastructure Advisory Council said in an August report. “When a cyber attack can deliver the same damage or consequences as a kinetic attack, it requires national leadership and close coordination of our collective resources, capabilities, and authorities.”
Amid the desire for public-private partnerships, there’s implicit skepticism about the government’s ability to do its part of the job. The SEC hardly reverses that impression, but, as alarming as its September disclosure was, the worst-case scenario did not materialize, and the regulator may still redeem itself.
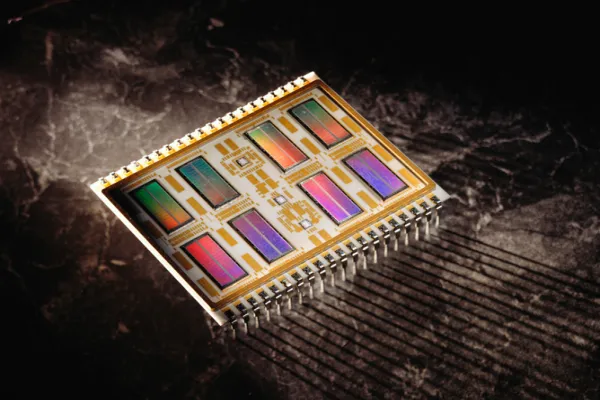
The SEC has embraced advanced technology as a remedy in the past. Turn back the clock to May 6, 2010, when the stock market suddenly plunged almost 1,000 points in intraday trading on the Dow Jones Industrial Average. The flash crash left no hesitation within the SEC that more data was needed to monitor markets. In 2013, the regulator implemented its Market Infrastructure Data Analytics System, allowing it to collect daily one billion records of trading data, time-stamped to the microsecond, former SEC Chair Mary Jo White said in a January 2014 address to a Securities Regulation Institute in California.
MIDAS was a precursor to the Consolidated Audit Trail, which gives the regulator a far more comprehensive view of stock and options trading. The SEC approved CAT in November, saying the system would be phased in to reporting requirements over the next two years.
In an effort to promote U.S. financial stability, President Barack Obama signed the Dodd-Frank Wall Street Reform and Consumer Protection Act in 2010. Dodd-Frank gave the Treasury Department’s Office of Financial Research broad powers to collect and analyze data from banks and other areas of the capital markets that might signal threats to the financial system.
In 2011 the Republican majority in Congress raised objections to the OFR’s broad mandate, questioning whether the office could be trusted to keep all that information secure. Spencer Bachus of Alabama, then chairman of the House Financial Services Committee, called OFR “a target-rich environment” for hackers.
OFR director Richard Berner said at a July 2011 hearing that it was protecting its data and would use information security measures consistent with best practices in government and private industry. “We are well aware of the threats to data security from the ‘black hat’ hacker community,” he said. “Preserving the security and integrity of OFR’s data is a mission-critical objective.”
Similar questioning hangs over the SEC’s “target-rich” CAT. Just as Berner shot down his critics, the technologists behind the winning bid to deploy CAT — a group led by Thesys Technologies — say they are armed and ready. Speaking September 21 at the annual Rosenblatt Securities Financial Technologies Summit, Shane Swanson, chief compliance officer of Thesys CAT, stressed that what will be “the largest single financial database in the world” has security built in “from the ground up.” In other words, the cybersecurity protecting CAT is not an after-thought or add-on, as would be necessary if it were a legacy system based on older technology.
Let’s hope that his confidence is justified. There is no margin for error for CAT, the SEC, and market integrity.