The next U.S. presidential election is a year away, but Richard Charnin is still reliving the voting of 2000, 2004 and 2008. He believes the counts were wrong.
Charnin is a quant. He has master’s degrees in mathematics and operations research and has worked on Wall Street, first as an applications developer at brokerage White, Weld & Co. in the 1970s, later as a consultant to major financial institutions.
Drilling into, and blogging about, election results, Charnin asserts that he has uncovered discrepancies that cannot be explained by randomness: ballots not tabulated, inconsistencies in the ways different types of machines count votes and too much variation between statistically valid exit polls and final, official tallies. “A clear pattern has emerged which confirms the overwhelming evidence of election fraud,” he writes in his 2010 book, Proving Election Fraud.
Despite his exhaustive documentation, Charnin is not universally endorsed. His evidence tends to show that Democratic candidates have been disadvantaged, and that invites accusations of partisanship. (Even Barack Obama’s decisive 53 percent of the 2008 popular vote was at least a few points shy of the reality, says Charnin.) In any enterprise that involves automated processing of items in the millions — be they bank checks, bill payments, standardized tests or tax forms — errors are inevitable and tolerated. But those error rates are in fractions of percentage points, well below what Charnin is alleging occurred in public elections.
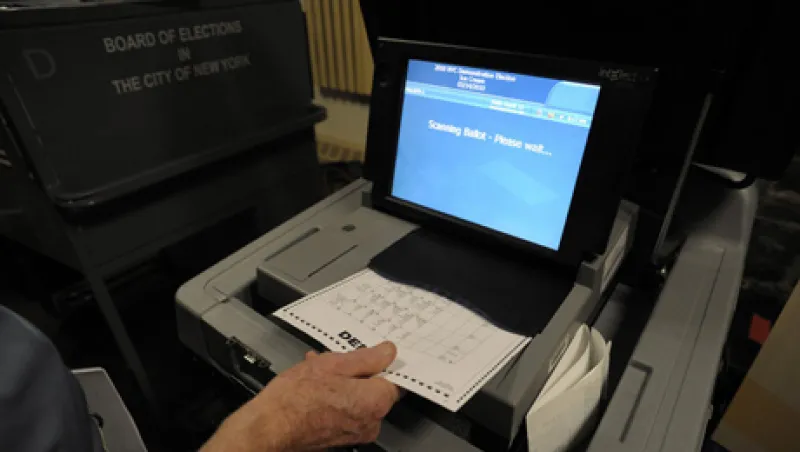
What cannot be disputed is that the U.S. voting infrastructure is fragmented, supervised with varying degrees of professionalism at the state and local government levels. The speed of the adoption of electronic voting and tabulation technologies, and the available competency to manage them, has also varied from place to place. Questions like those raised by Charnin have become increasingly persistent since the 1960s, paralleling the spread of automation. Similar inconsistencies and controversies have surfaced in Brazil, Germany, Mexico and elsewhere.
Some of the loudest alarms about automated voting — about the rush to adoption and vulnerability to security breaches, errors and manipulation — have come from the computer science community. Since, and in some cases before, the protracted Florida vote-counting that gave the 2000 presidential election to George W. Bush over Al Gore, people like Johns Hopkins University computer science professor Avi Rubin and Peter Neumann of the SRI International Computer Science Laboratory were calling for closer scrutiny and controls.
Many such experts cringed at suggestions that the technology — whether in the form of touch screens or optical document scanning — was not only secure and reliable enough for mass consumption but also extendable to remote or online voting. The Vulnerability Assessment Team at the U.S. Department of Energy’s Argonne National Laboratory hyperlink: (http://www.anl.gov/Media_Center/News/2010/news101026.html)in Illinois recently demonstrated how a touch-screen terminal could be hacked by remote control using components purchased for $26. Team leader Roger Johnston said that “a wide variety of electronic voting machines” are likely to be similarly exposed.
But technologists are also in the solutions business. A cadre that includes renowned cryptologist David Chaum and Massachusetts Institute of Technology professor Ronald Rivest, a co-founder of data security pioneer RSA, is responsible for Scantegrityhyperlink:(http://www.scantegrity.org/), which layers cryptographic coding on top of the common optical-scan method. The town of Takoma Park, Maryland, first deployed Scantegrity in 2009, with no glitches or security breaks. “This is real, not a demonstration,” asserts Chaum. Scantegrity preserves voter anonymity while addressing concerns about data integrity and auditability to resolve disputes, says Rivest.
Electronic voting is just as real — on a sizable scale, tightly audited, with a clean operational record — in corporate proxy balloting. Brokerage servicer Broadridge Financial Solutions introduced e-voting on its ProxyEdge platform 14 years ago. That website recorded 25.4 billion votes in the February-May 2011 proxy season, and after the March introduction of a mobile version, 150,000 shareholders cast votes via handheld devices. Broadridge investor communications product manager Joseph Vicari says the fact that “proxy is a pillar of corporate America” warranted a high degree of care; he adds that the encryption security is equal to that of electronic commerce.
If it works in corporate governance, why not civic democracy? Rivest cautions that proxy votes are rarely as close and contested as, say, Bush versus Gore was, so perhaps systems like ProxyEdge have yet to be tested in that way. That said, technology proved to be a solution, which is hopeful, because the political system sorely needs one. • •